Vulnerability Trends Summary
As part of our monthly vulnerability trends, this report shows the monthly top 10 trends on security vulnerabilities and how hackers, malware, and exploit kits are exploiting those vulnerabilities. To demonstrate, we assign vulnerability trends value as a percentage of how each vulnerability is significantly gaining the attention of cybersecurity communities, attackers, together with malware. In either case, companies can benefit from the report to have more cyber threat insights and relatively anticipate attacks wave that might target their public assets in the following months.
Subscribe to the monthly vulnerability digest report by clicking here.
The following chart shows the trends.
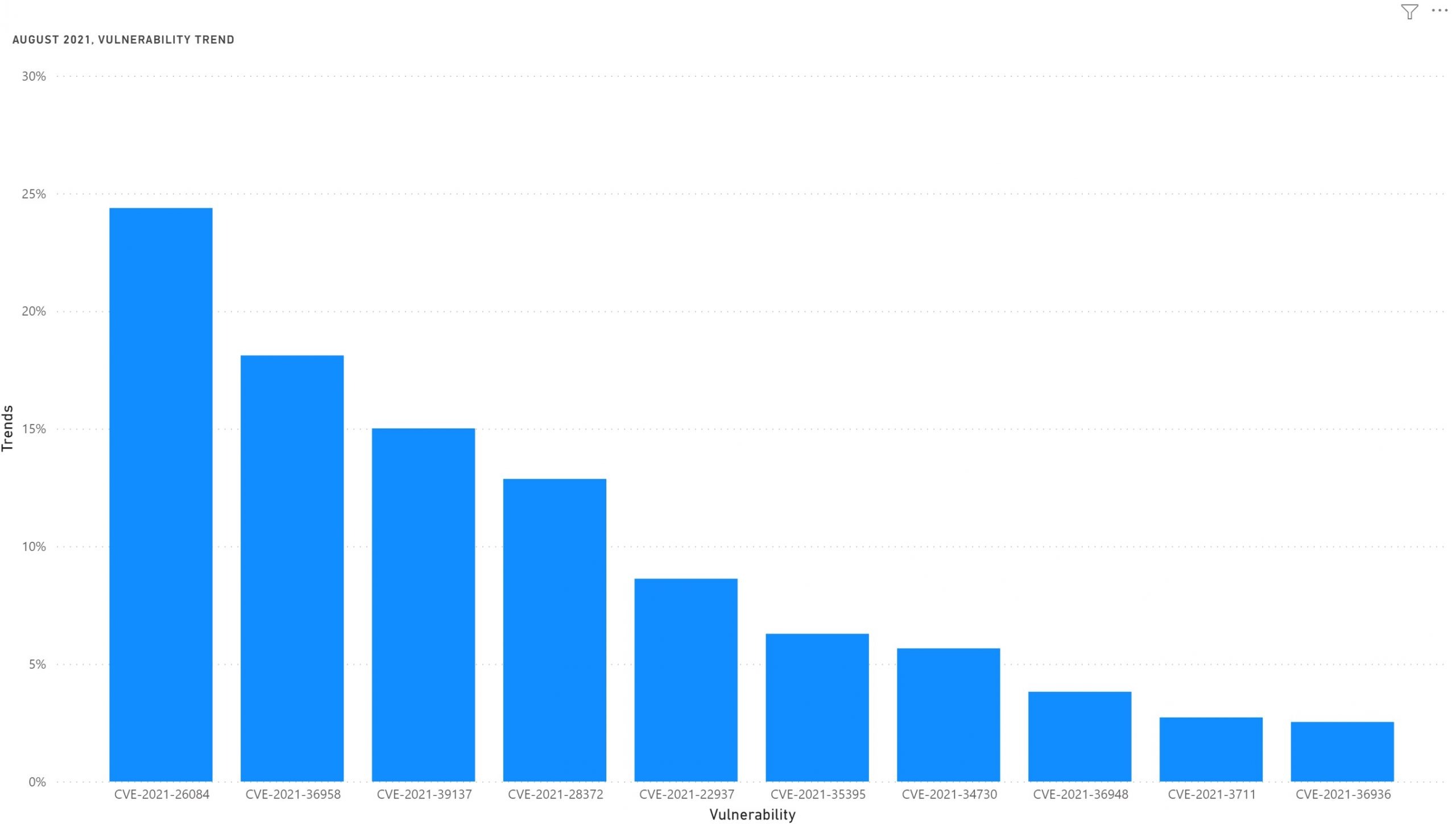
In August 2021 there are no major vulnerabilities that hijacked all community attentions. However, still critical vulnerabilities are hitting the Windows Print Spooler service.
Other important vulnerabilities were disclosed in some IoT devices, Cisco Routers, and OpenSSL.
The following table shows the details of the trends.
| CVE | Vulnerability | Publish Date | Exploited | Trends* |
| CVE-2021-26084 | Confluence Server RCE | 26/08/2021 | Yes | 24% |
| CVE-2021-36958 | RCE in Windows Print Spooler Service | 11/08/2021 | Yes | 18% |
| CVE-2021-39137 | Consensus Vulnerability in Go-Ethereum | 24/08/2021 | No | 15% |
| CVE-2021-28372 | Credential Leak in TUTK device | 17/08/2021 | Yes | 13% |
| CVE-2021-22937 | Code Execution in Pulse Connect Secure | 05/08/2021 | Yes | 9% |
| CVE-2021-35395 | Realtek APRouter SDK Remote Code Execution | 16/08/2021 | Yes | 6% |
| CVE-2021-34730 | Denial of Service in Cisco Routers | 18/08/2021 | No | 6% |
| CVE-2021-30563 | Elevation of Privilege in Windows | 10/08/2021 | No | 4% |
| CVE-2021-33910 | Code Execution in OpenSSL | 24/08/2021 | No | 3% |
| CVE-2021-36936 | RCE in Windows Print Spooler | 10/08/2021 | No | 2% |
Subscribe to the monthly vulnerability digest report by clicking here.
1. CVE-2021-26084 Confluence Server RCE
OGNL (Object-Graph) injection vulnerability exists that would allow an authenticated user, and in some instances an unauthenticated user, to execute arbitrary code on a Confluence Server or Data Center instance.
2. CVE-2021-36958 RCE in Windows Print Spooler Service
Remote Code Execution vulnerability exists in Windows Print Spooler service. This vulnerability is different than the previous ones.
3. CVE-2021-39137 Consensus Vulnerability in Go-Ethereum
The library go-ethereum is the official Go implementation of the Ethereum protocol. In affected versions, a consensus vulnerability in go-ethereum (Geth) could cause a chain split, where vulnerable versions refuse to accept the canonical chain.
4. CVE-2021-28372 Credential Leak in TUTK device
ThroughTek’s Kalay Platform 2.0 network allows an attacker to impersonate an arbitrary ThroughTek (TUTK) device given a valid 20-byte uniquely assigned identifier (UID). This could result in an attacker hijacking a victim’s connection and forcing them into supplying credentials needed to access the victim’s TUTK device.
5. CVE-2021-22937 Code Execution in Pulse Connect Secure
A vulnerability in Pulse Connect Secure could allow an authenticated administrator to perform a file write via a maliciously crafted archive uploaded in the administrator web interface.
6. CVE-2021-35395 Realtek APRouter SDK Remote Code Execution
Buffer overflow vulnerability exists in Realtek ARPRouter SDK that causes remote code execution in the devices that utilize this SDK.
7. CVE-2021-34730 Denial of Service in Cisco Routers
A vulnerability in the Universal Plug-and-Play (UPnP) service of Cisco Small Business Routers could allow an unauthenticated, remote attacker to execute arbitrary code or cause an affected device to restart unexpectedly, resulting in a denial of service (DoS) condition.
8. CVE-2021-30563 Elevation of Privilege in Windows
An actively exploited vulnerability exists in the Windows Update Medic service that allows an elevation of privileges.
9. CVE-2021-33910 Code Execution in OpenSSL
In OpenSSL SM2 decryption code has a buffer overflow that leads to code execution when calling the API function to decrypt SM2 encrypted data.
10. CVE-2021-36936 RCE in Windows Print Spooler
Again, a vulnerability exists in the Windows Pring Spooler servicer that leads to remote code execution. The relation with the last month’s RCE (CVE-2021-34527) is not clear.
| CVSS Rate | 9.8 Critical |
| Exploited | No |
| Links | https://msrc.microsoft.com/update-guide/vulnerability/CVE-2021-36936 |
ScanTitan is the leading website security portal that offers website vulnerability scanning, website malware scanning, uptime monitoring, cyber brand monitoring, defacement monitoring, and continuous threat monitoring and alerting.
Now you can find the latest Scantitan promotions through our official coupon store.
Fuente obtenida de: https://scantitan.com/blog/monthly-vulnerability-digest/august-2021-vulnerability-trends/